IT asset management (ITAM) is a set of business management processes that support strategic decision-making, optimize spending, and lifecycle management for the IT framework. At its core, ITAM has a combination of inventory, financial, and contractual functions.
The IT asset management procedure usually entails collecting a comprehensive inventory of an organization’s network assets – both hardware and software – and then utilizing that data to make educated business decisions regarding IT-related purchases and redistribution.
An IT asset is defined as any corporation-owned intel, hardware, or system that has been or is currently being utilized throughout a company’s business endeavors.
As new advancements in technology are developed and made available, you may find that it’s becoming increasingly difficult to identify what internal IT assets are present in your system, where they’re stored, and who is responsible for keeping track of them.
Assets tend to get tracked by a slew of individuals and are found in several different locations, with no sole owner or collecting tool to centralize this valuable information. The solution to this problem is to formulate and adhere to the best IT asset management practices.
While IT asset management is an excellent way to create an asset inventory, its primary function is to continually utilize collected data to maximize returns, minimize risk, and drive increased business value. ITAM brings all these benefits to the table by avoiding expendable asset purchases and using current assets to their full potential.
If your company seeks to improve software management post-merger and acquisition, let this infographic serve as your comprehensive guide in “The 5S” methodology of IT asset management.
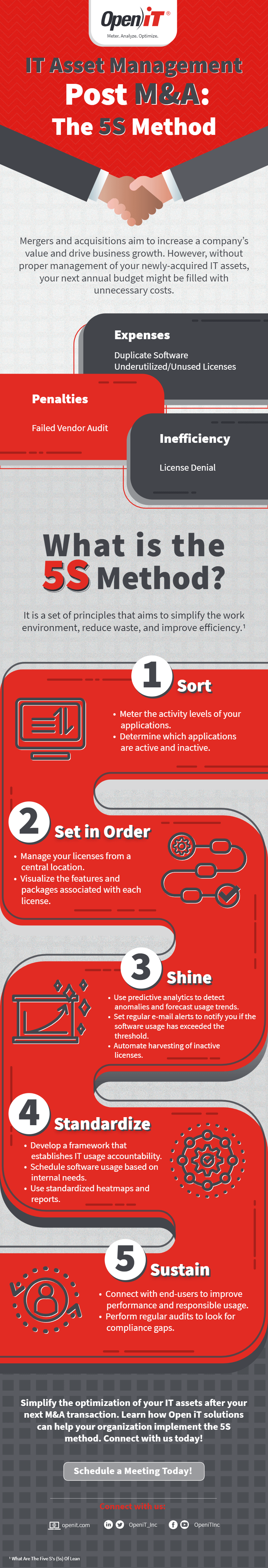
Infographic Source: https://openit.com/resources/infographics/it-asset-management-post-ma-the-5s-method/
